

Its Your Investigation. What’s Your Solution?
All investigations are not created equal. Here’s how to determine what you need to crack your case through Access Data….
All investigations are not created equal.
Here’s how to determine what you need to crack your case.
STEP 1: What’s your role?
CFO, Corporate Counsel,
IT Operations Manager,
Litigation Support Manager,
Legal Operations Manager
or Paralegal


IT incident responder, legal
and HR administrator,
litigation specialist,
digital forensic analyst or
employee of a federal agency
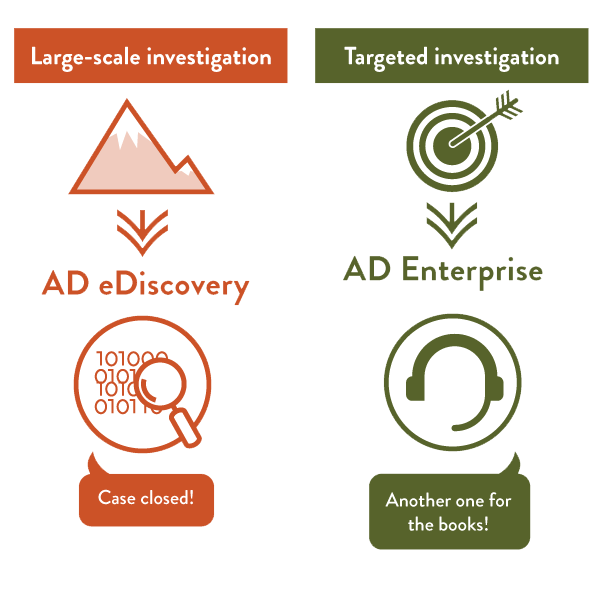
STEP 2: What’s your mission, should you choose to accept it?
To conduct a large scale
compliance investigation
that requires end-to-end
e-discovery.


To conduct a targeted
investigation into employee
misconduct.
STEP 3: What’s your solution?
STEP 4: How do I use this solution?
Schedule large audits of
computers, network shares,
and data repositories.
Build complex criteria to
address data retention, right
to be forgotten, PII, credit card
audits, e-discovery, and more.
Search for key documents
or collect reactive documents
for further investigation.
Conduct forensics investigations
targeting 1-20 computers or
large scale incident response to
thousands of computers focusing
only on volatile data.
Handle a deeper, more technical
investigation than Access Data eDiscovery.
Deal with a wide array of file
types and data sources.
STEP 5: Check yourself.
Use Access Data eDiscovery if it’s:
A web-based, large scale review.


Use Access Data Enterprise if it’s:
A targeted forensics investigation.
THE RESULT
Review of collected data on
a web-based review platform,
where you can apply complex
visualization, data analytics,
and document review tools
to pinpoint key documents.
The restoration of partially
deleted or volatile data,
fragmented files, and hidden
processes.
HOW AD EDISCOVERY AND
AD ENTERPRISE CAN HELP YOU.
Both products ensure full coverage across all of your investigative requirements. In a typical workflow, you may use AD eDiscovery for large scale data sweeps and AD Enterprise for targeted investigations of key computer systems or high profile executives.
Both ensure you have the depth and breadth to satisfy legal opponents, external regulators, general counsel, and compliance.
Source “http://accessdata.com/blog/its-your-investigation-whats-your-solution”
