SOURCE CODE REVIEW SERVICES
Source Code Review: Overview
Source Code Review (SCR) is a systematic & Security examination of the Source Code of Application and Software. It looks for Security Loop Holes, Bugs that may have been planted and overlooked during Application and software development.
Sometimes, certain Applications and Software may contain vulnerabilities that can aid attackers to extract vital information and may lead to loss of intellectual property & Secure Data. Reviewing Source Code helps to verify the implementation of key security controls. It also looks for design flaws and discovers hidden vulnerabilities in any application and software.
Source code analysis not only distinguishes which proclamation on which line of code is helpless but at the same time can recognize the polluted variable that represents the vulnerability. Along these lines, it represents the spread from the underlying driver, to the final product. This furnishes application developers with a conclusion-to-end outline of each example of vulnerability, enabling them to rapidly comprehend the idea of the issue. Also, check the source code analysis tool.


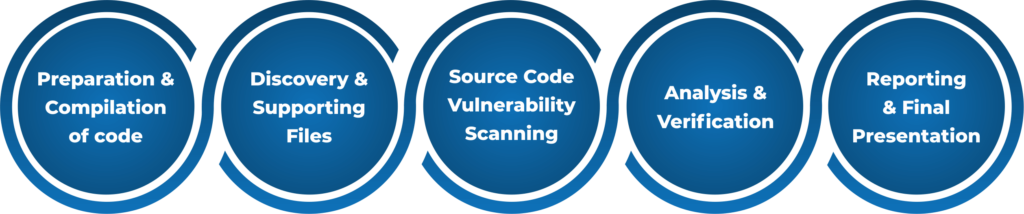
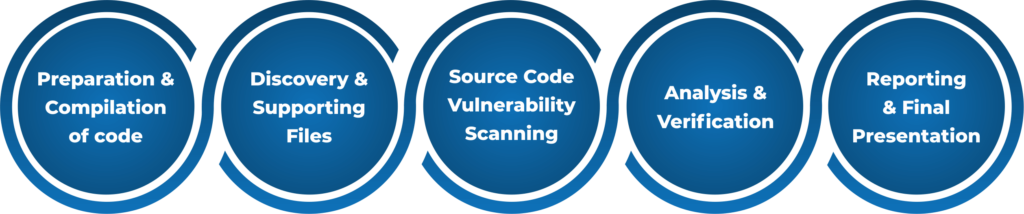
Source Code Review Methodology
More about Source Code Review
Source Code review discovers hidden vulnerabilities, design flaws, and verifies if key security controls are implemented. Many a time software and applications contain bugs and vulnerabilities, which creates the possibility that the product might face potential attacks from attackers trying to take advantage of such flaws. This can give attackers an inside view of important information (data Leakage) and assets.
Many a time the development and deployment phase of an application is hurried upon for swift completion of the project. In such situations, there remains the high possibility that the product might not be put through proper security tests. As a result, clients using those products are more likely to fall victim to attackers. Such applications should be passed through a rigorous review process (Vulnerability Assessment) to detect the vulnerabilities, present in them
Source Code Review: Approach
The following steps are identified with the procedure involved:
- Source Code Review starts with a review of the software and the coding process that went into making the software. The process includes discussion pertaining to the software, with the development team. The developers are required to respond to an extensive list of questions related to security for the purpose of identifying security design issues.
- The second step involves the preparation of a code review plan.
- The third step involves identifying composing data placed within the code. Another important task is to find bad coding techniques which make it easier for attackers to gain access to the software. Upon completion of the analysis, the next step involves the verification of existing flaws. Every possible security vulnerability is listed and remedial steps are introduced to improve the development process that software goes through.
The exhaustive process of finding bugs through Source Code review helps to detect the vulnerable line of code. Upon doing so, it exposes the root of the problem. This gives the Application Developers a complete general idea of each occurrence of susceptibility, allowing them to swiftly comprehend the temperament of the hitch.
After completion of the code review, we’ll provide you with complete details of cyber security vulnerabilities as well as suggestions to improve the overall development process.
Source Code Review – Challenges
Since applications contain bugs; there is a chance that an attacker may have the capacity to abuse some of them to affect or access your information resources and abilities. Web applications specifically are more be influenced by these vulnerabilities, as they are much of the time created and sent rapidly underway in brief terms without adequate time spent in security testing. We have a thorough system for auditing web application code. Our survey procedure is particularly custom fitted to discover vulnerabilities that ordinarily happen in applications. We utilize a blend of both computerized and manual strategies to lead a source code survey. Using tools, for example, Checkmarx and Fortify, we can get vulnerabilities crosswise over expansive code-bases, and then limited our concentration onto security-particular modules of code, (for example, those actualizing encryption or approval) and additionally check for business rationale issues.
eSec Forte Technologies: Source Code Review Company
Applications and software should be put through Source Code Reviews even as early as during the initial phase of project development. Experts at eSecForte stress the importance of performing such Reviews right from the early stages of project development. It is because the expenses conjured during the development stage of software is less as compared to the deployment or implementation phase of the product. Source Code Reviews can be done both on-site and remotely, according to the convenience of the client. We are among the top-rated Code Review Companies in India.
eSec Forte Technologies is a CMMi Level 3 | ISO 9001:2008 | ISO 27001-2013 certified Cyber Security Audit Company and IT Services Company with service offerings in Information Security like VAPT Services, Penetration Testing Services, Vulnerability Assessment Services, Amongst our clients we proudly count Government Organizations, Fortune 1000 Companies, and several emerging companies.
We are headquartered in Gurugram, Mumbai, Delhi, Bangalore – India & Singapore. Contact our sales team @ +91 124-4264666 you can also Drop us an email at [email protected] for Source Code Review Services.
