

No Rate Limit
Vendor of the product(s): Rubicon Communications, LLC (Netgate).
Product Name:Netgate
Vendor Mail –ID: [email protected]
Version – exact ver of the product which is vulnerable:All Pfsense CE version affected Tested on 2.6.0
Affected component(s) :Password change functionalities
Attack vector(s):NA
Suggested description of the vulnerability for use in the CVE :No rate limit on add user in Pfsense CE
Discoverer(s)/Credits – :Dipendar Sharma
Overview:-
All Pfsense CE firewall vulnerable to No rate limit
A attacker can create multiple malicious users in firewall and also attacker control on firewall remotely via ssh with malicious user name and password credentials its critical issue for a organizations.
Details
No rate limit is a flaw that doesn’t limit the number of attempts one makes on a website server to extract data. It is a vulnerability that can prove to be critical when misused by attackers.
Poc Details:-
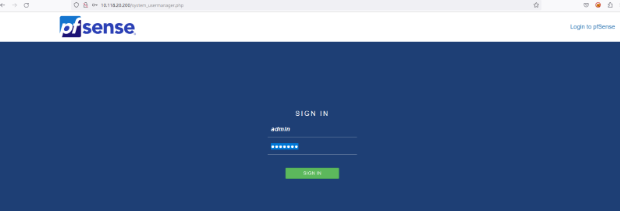
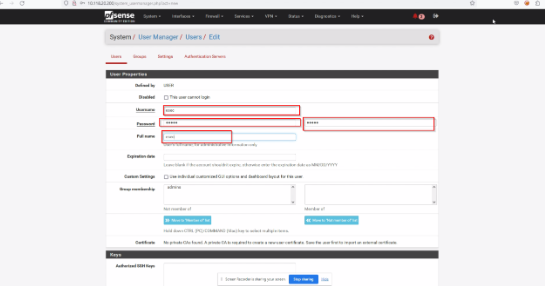
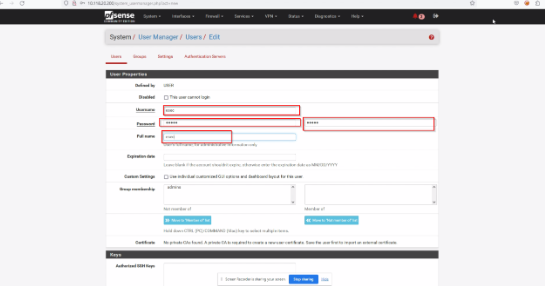
Step-1 Login to the application as admin:pfsense via visiting http://10.118.20.200/system_usermanager.php?act=edit&userid=2
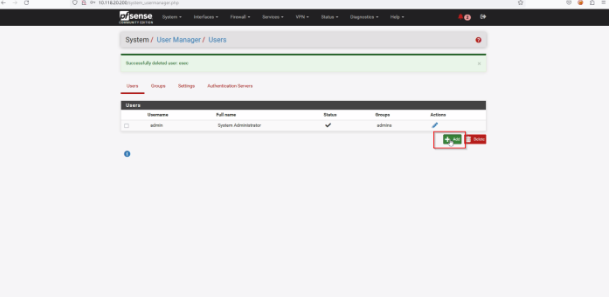
Step-2 Click on user manager and then click add
Step-3 Now enter username and password for new user
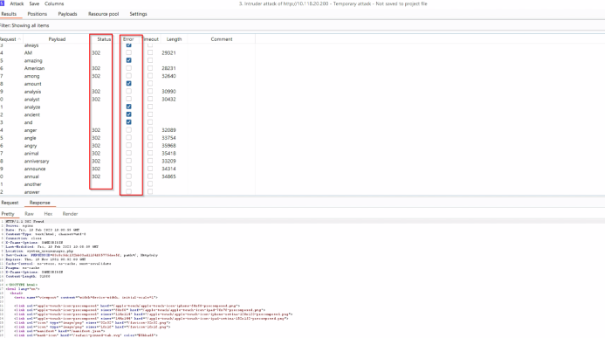
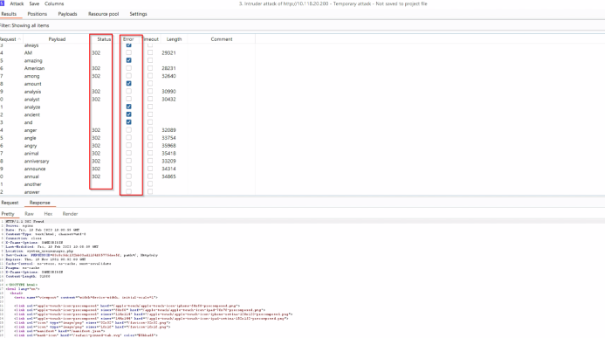
Step-4 In this step we will intercept the request
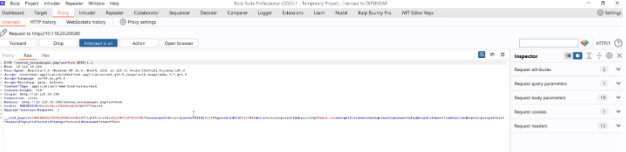
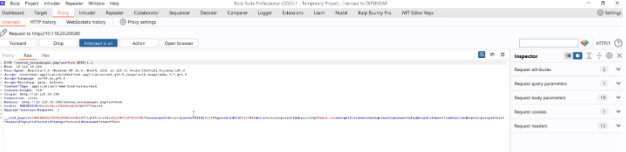
Step-5 In this step we will set payload and after that start attack. In this step we will set payload and after that start attack.
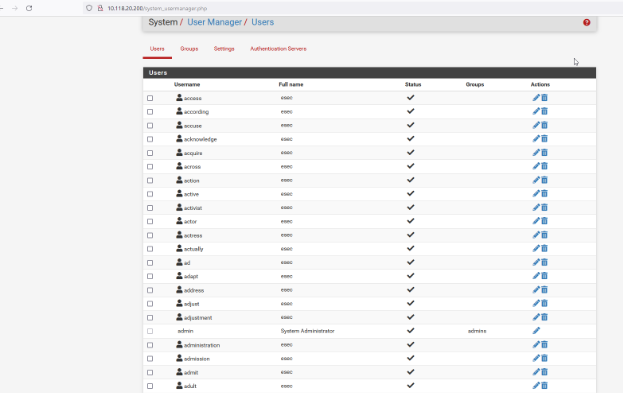
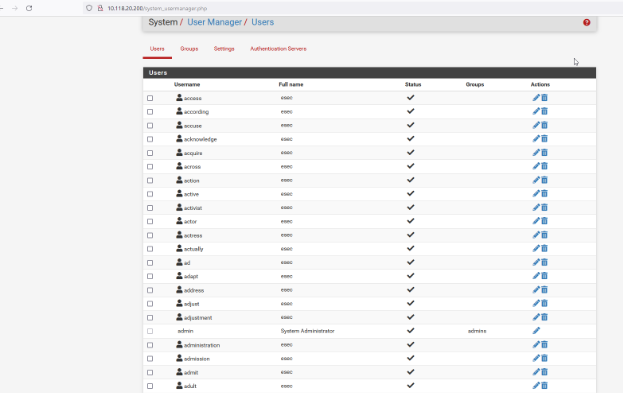
Step-6 Finally we had create multiple malicious users with password 123
Affected Environments
Pfsense CE all version
Prevention
A product’s design should require adherence to an appropriate password policy. Specific password requirements depend strongly on contextual factors, but it is recommended to contain the following attributes:
Enforcement of a minimum and maximum length
Restrictions against password reuse
Restrictions against using common passwords
Restrictions against using contextual string in the password (e.g., user id, app name)
Depending on the threat model, the password policy may include several additional attributes.
Complex passwords requiring mixed character sets (alpha, numeric, special, mixed case)
Increasing the range of characters makes the password harder to crack and may be appropriate for systems relying on single factor authentication.
Unfortunately, a complex password may be difficult to memorize, encouraging a user to select a short password or to incorrectly manage the password (write it down).
Another disadvantage of this approach is that it often does not result in a significant increases in overal password complexity due to people’s predictable usage of various symbols.
Large Minimum Length (encouraging passphrases instead of passwords)
Increasing the number of characters makes the password harder to crack and may be appropriate for systems relying on single factor authentication.
A disadvantage of this approach is that selecting a good passphrase is not easy and poor passwords can still be generated. Some prompting may be needed to encourage long un-predictable passwords.
Randomly Chosen Secrets
Generating a password for the user can help make sure that length and complexity requirements are met, and can result in secure passwords being used.
A disadvantage of this approach is that the resulting password or passpharse may be too difficult to memorize, encouraging them to be written down.
Password Expiration
Requiring a periodic password change can reduce the time window that an adversary has to crack a password, while also limiting the damage caused by password exposures at other locations.
Password expiration may be a good mitigating technique when long complex passwords are not desired.
