CyberObserver
Continuous Cyber Security Management and Awareness Solution


CyberObserver: Overview
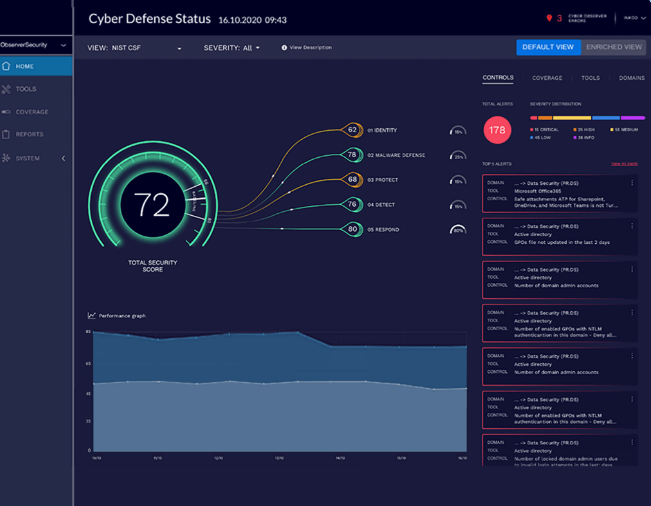
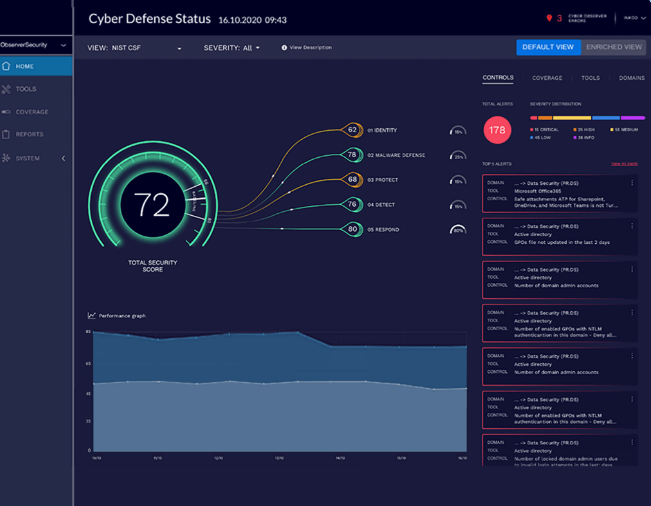
Cyber Observer is a Security Management and awareness solution. It continuously measures the cybersecurity status of an organization’s security environment by retrieving and analyzing Critical Security Controls (CSCs) from relevant security tools. The comprehensive information empowers CISOs and executives to make insightful and timely decisions to ensure the cybersecurity of the organization. Developed for CISOs, InfoSec, and IT managers, Cyber Observer provides extensive cybersecurity understanding for all stakeholders. By connecting to the security and related third-party vendor tool suite, Cyber Observer provides insights and recommendations to empower effective enterprise cyber defense. Empowered with comprehensive awareness, you can easily identify weaknesses, reduce mean time to detect, prevent breaches, drive strategic planning, and report to executive stakeholders.
Four Layers of Cybersecurity
Organizations fortify themselves with an abundance of security technologies then may struggle to determine the enterprise level of cybersecurity achieved. Cyber Observer delivers a single-pane-of-glass solution displaying performance data that proactively provides improvement recommendations in near real-time. This single view of enterprise-wide cybersecurity allows the organization to deliver the level of security required, meeting both compliance and business risk needs.
CyberObserver Features
CyberObserver Pricing
Its cost is dependent upon the license you wish to choose as it gives you various options. The detailed price structure can be availed through Value Added Distributor eSec Forte Technologies who are well versed with all the data associated.
Contact us today to learn more about our products and services.
We are headquartered in Gurugram & Regional Offices in Mumbai, Delhi, Bangalore – India.




