

WordPress Duplicate Page Plugin – Stored Cross-Site Scripting (XSS)
Title: Responsible Vulnerability Disclosure Stored Cross-Site Scripting (XSS) CVE-2021-24681: – Stored Cross-Site Scripting (XSS) Vulnerability in WordPress Duplicate Page Plugin (Affected Plugin Version Number < 4.4.3).
INTRODUCTION
WordPress is a content management system (WCM) i.e., it is a tool that organizes the whole process of creating, storing, and showcasing web content in an optimal way. WordPress started its journey as an improvement tool to enhance the regular typography of day-to-day writing. But it was taken as a blogging tool and as we reach the last quarter of this year WordPress stands strong as the most used WCM system used and that also not only in the blogging community. WordPress is completely an open-source tool and is still being updated very frequently.
eSecForte Technologies Security Researcher – Nikhil Kapoor found a Stored Cross-Site Scripting (XSS) vulnerability in the WordPress Duplicate Page Plugin, and it has been assigned CVE-2021-24681 by the WPScan.
Description: Cross-Site Scripting (XSS) attacks are a type of injection, in which malicious scripts are injected into otherwise benign and trusted websites. XSS attacks occur when an attacker uses a web application to send malicious code, generally in the form of a browser side script, to a different end user. Flaws that allow these attacks to succeed are quite widespread and occur anywhere a web application uses input from a user within the output it generates without validating or encoding it.
Platform/Product: WordPress Duplicate Page Plugin – Affected Plugin Version Number < 4.4.3
Vulnerability Name: Stored Cross-Site Scripting (XSS)
Affected Component:
Attack Type:
Impact:
Attackers can execute scripts in a victim’s browser to hijack user sessions, deface websites, insert hostile content, redirect users, hijack the user’s browser using malware, etc.
Recommendation:
Steps to Reproduce #:-
- The preferred option is to properly escape all untrusted data based on the HTML context. Include data escaping techniques in their applications.
- Use positive or “white-list” input validation to protect against XSS.
- Use HTML & URL encoding for applications that accept special characters and meta tags. Such validation should decode any encoded input, and then validate the length, characters, and format on that data before accepting the input.
- Client-side and server-side validation should be implemented. Server-side validation is mandatory.
Method of Exploitation
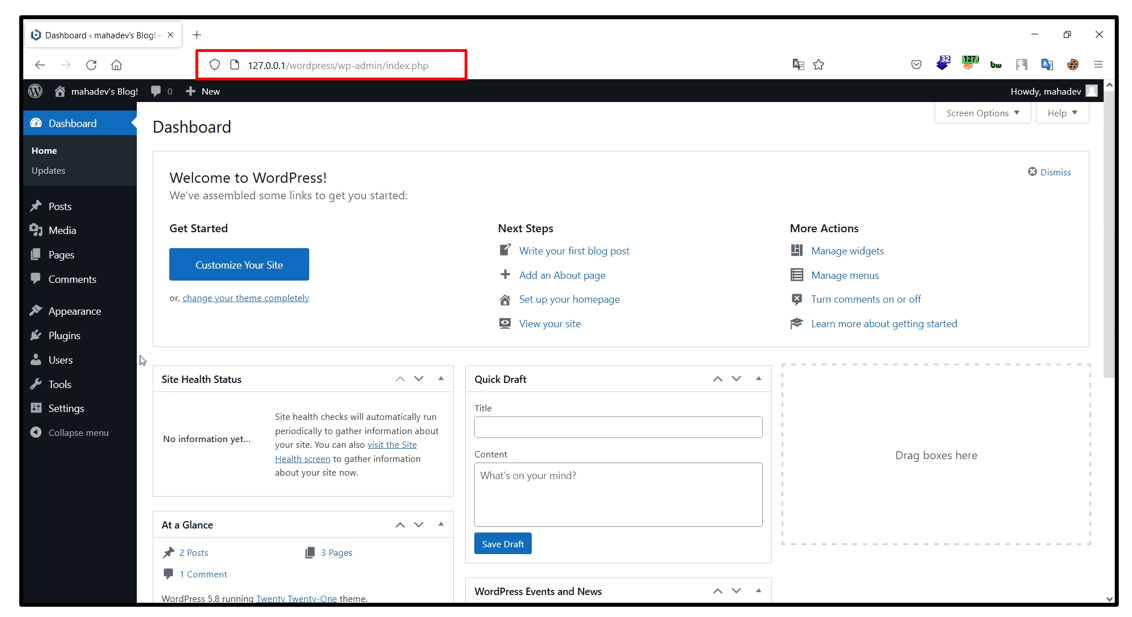
1. Install WordPress and Go to the dashboard.
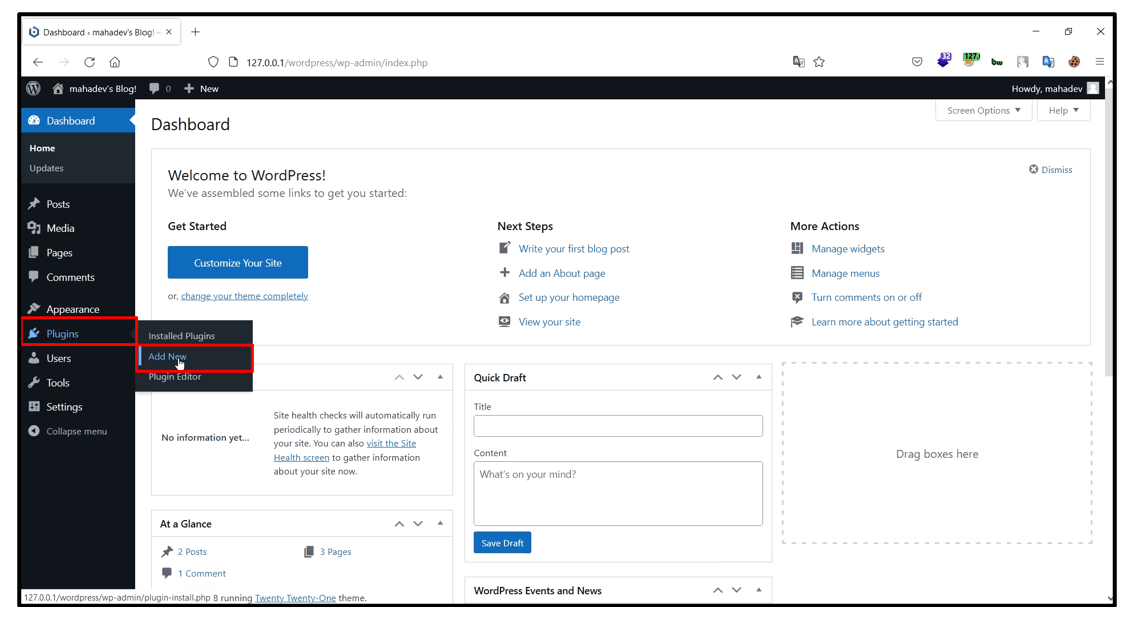
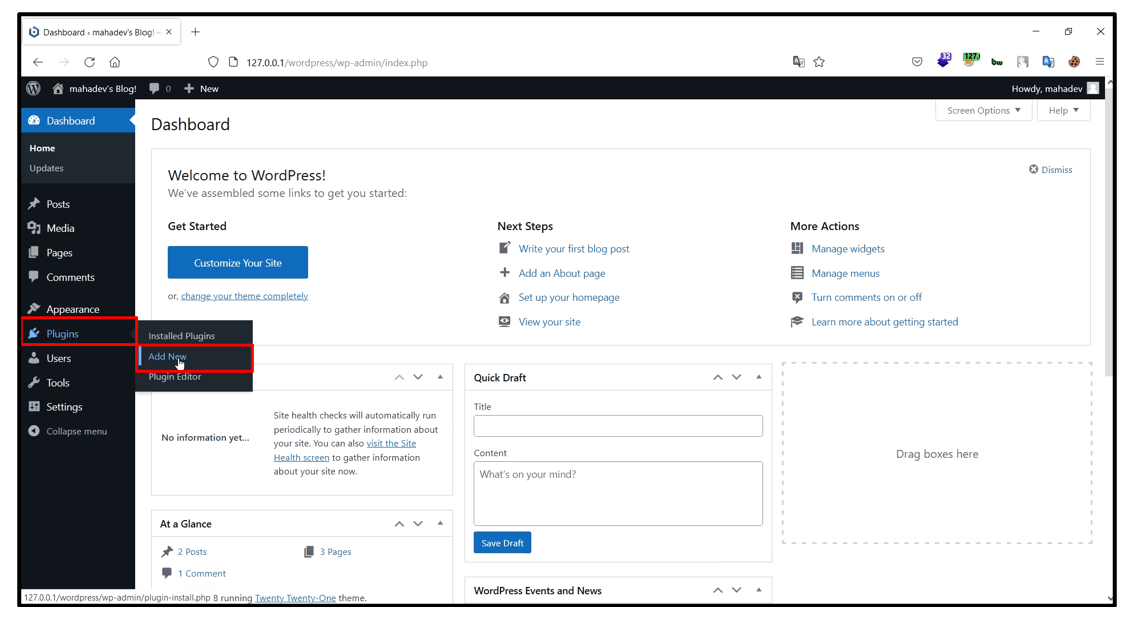
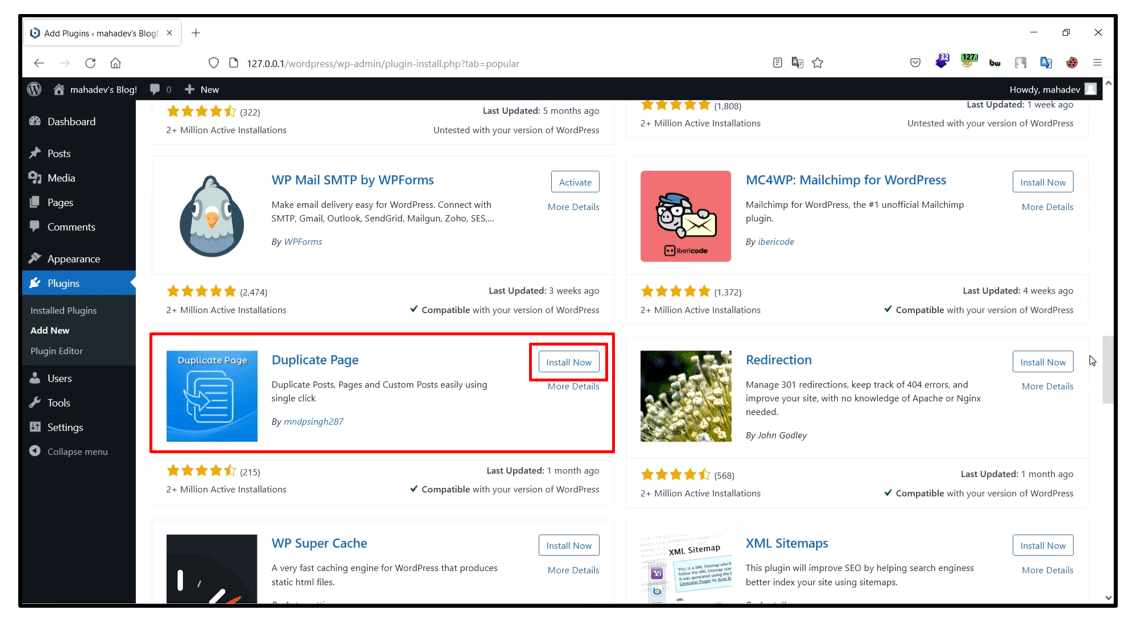
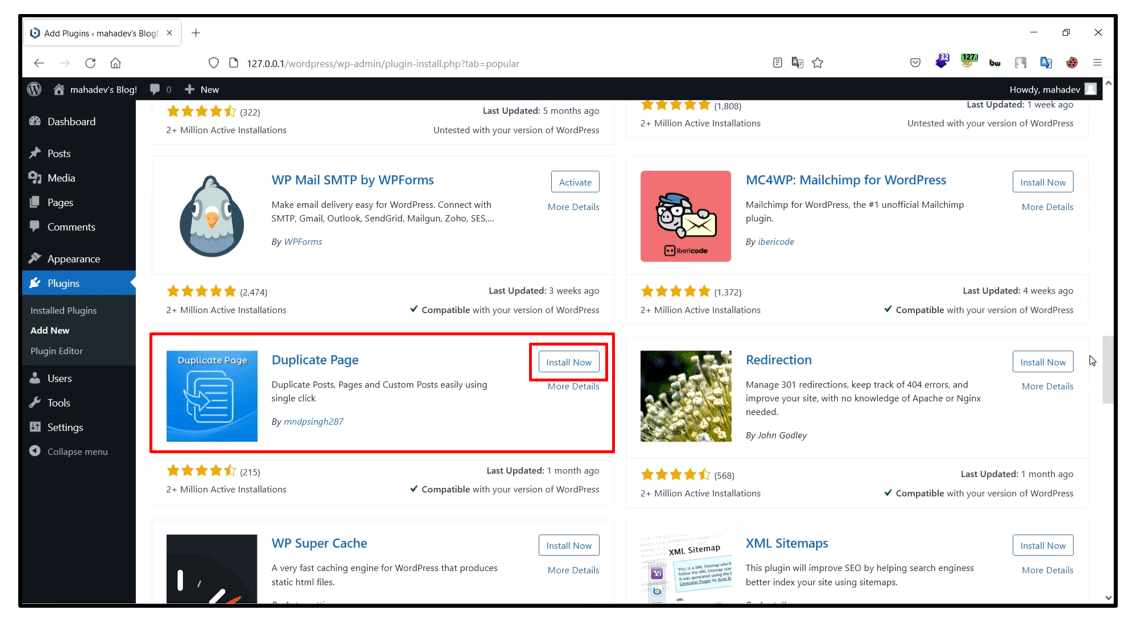
2. Now go to Plugin and select Add New.
3. Now Install and Activate Duplicate Page Plugin.
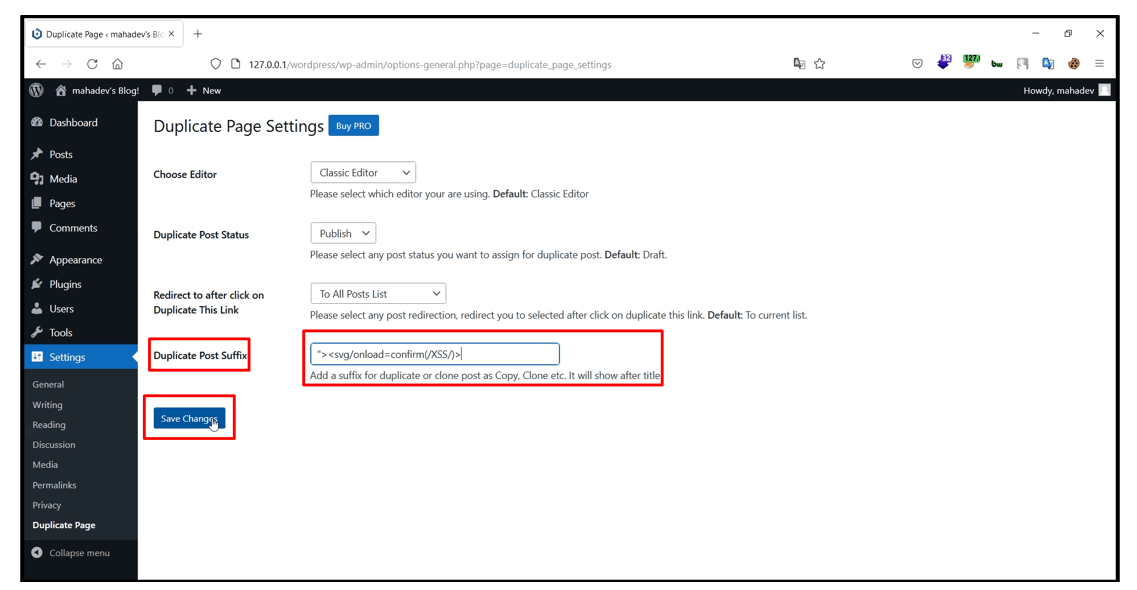
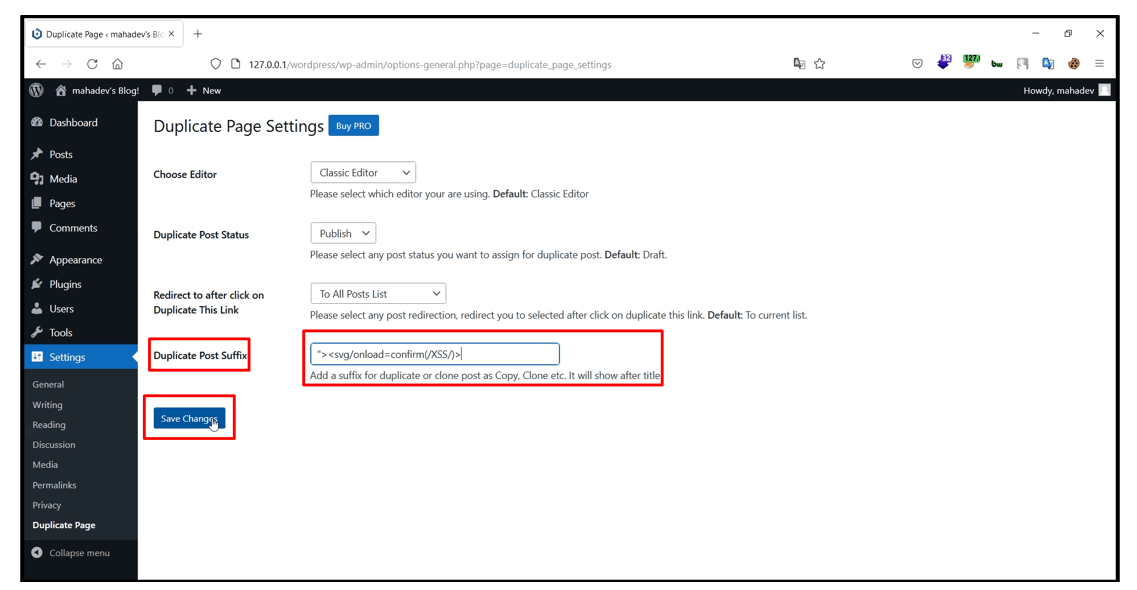
4. Now go to settings > Duplicate Page.
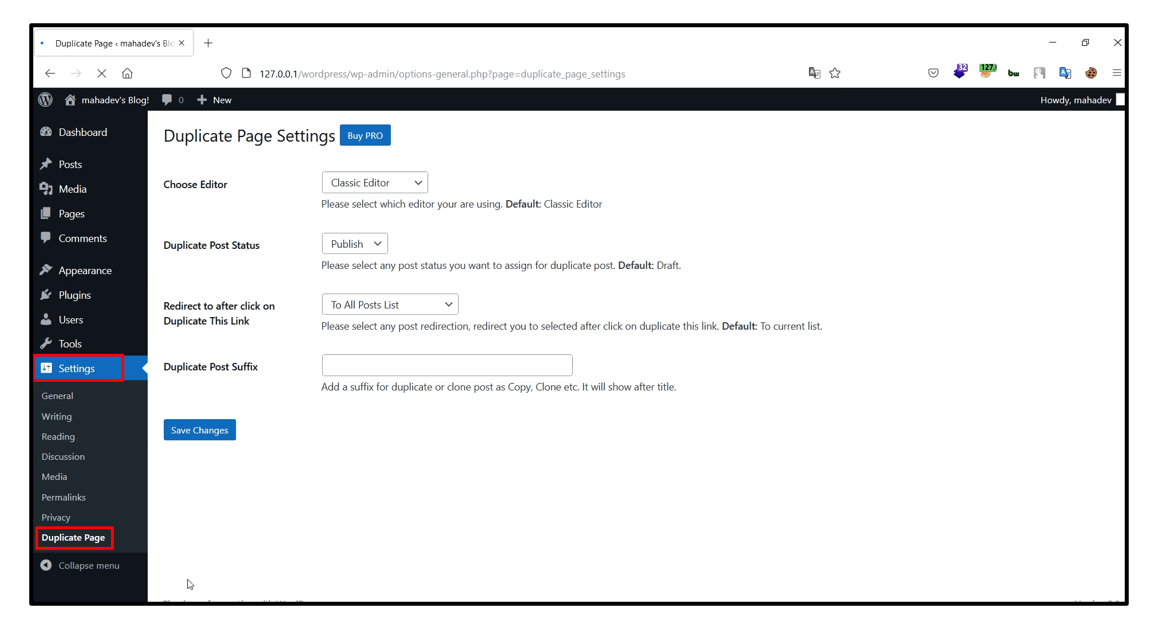
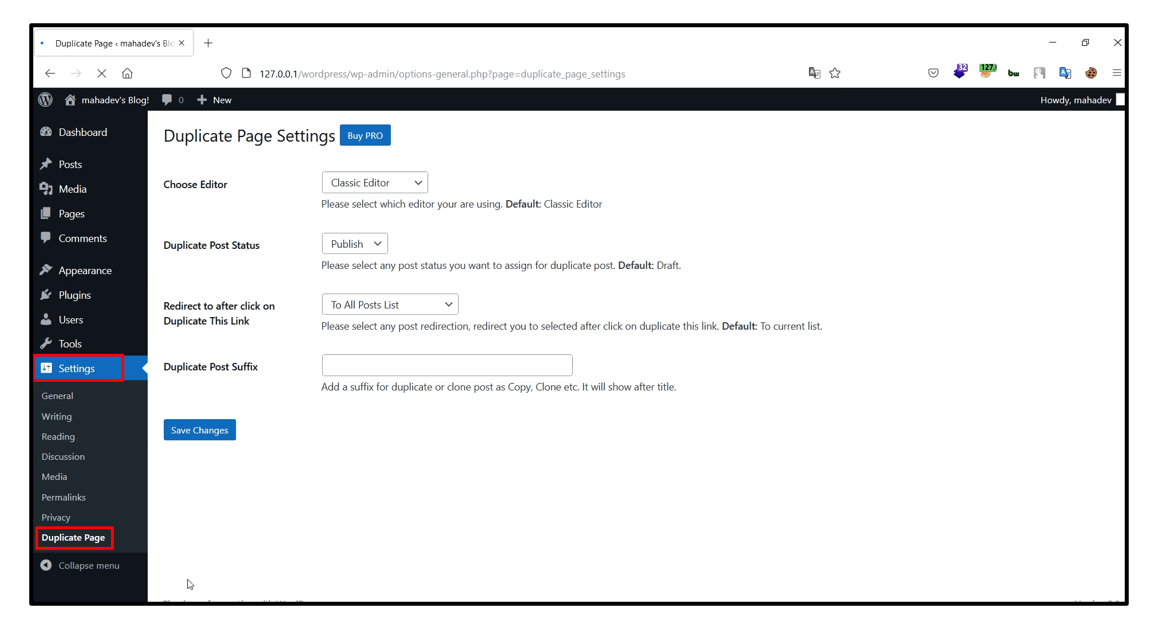
5. “Duplicate Post Suffix” Input Field is Vulnerable to Stored Cross-Site Scripting Vulnerability (XSS). Enter XSS Payload and click on save changes button.
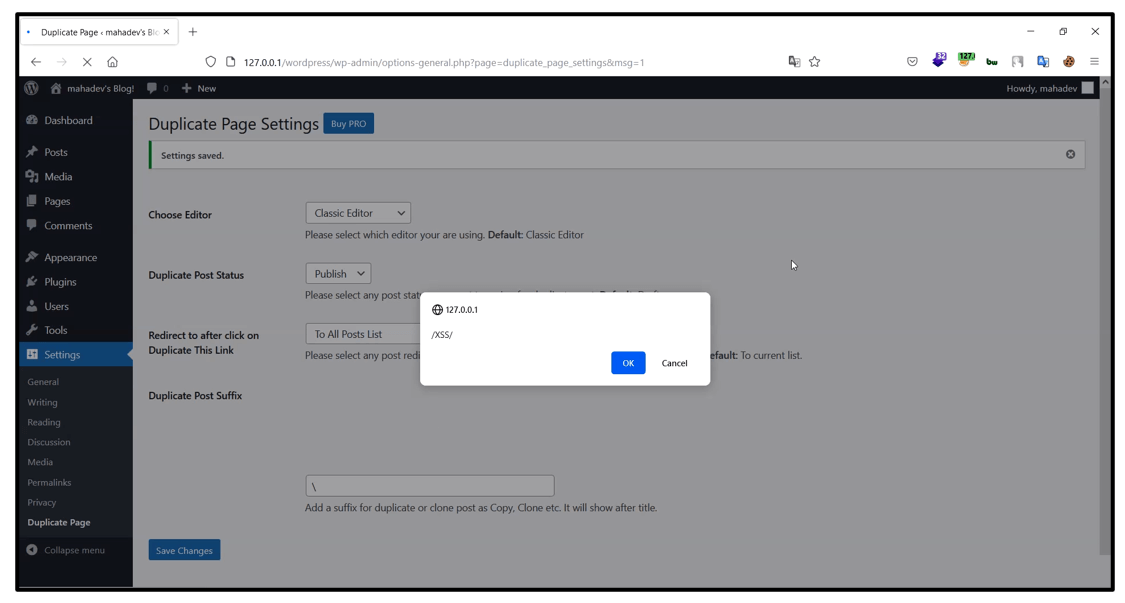
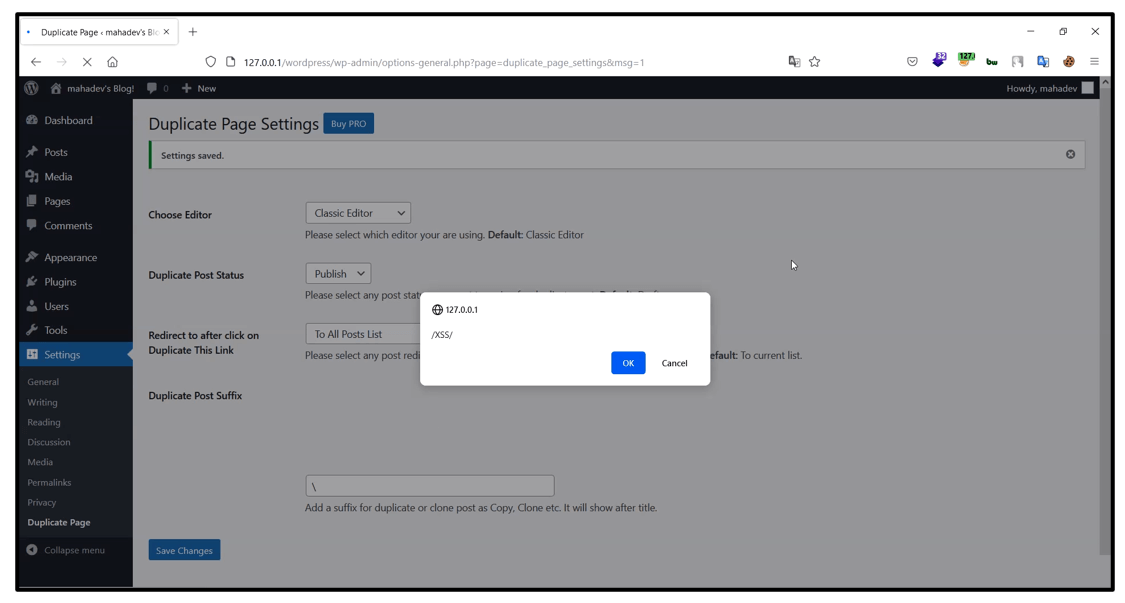
6. You will observe that the payload successfully got stored into the database and when you are triggering the same functionality at that time JavaScript payload is executing successfully and we are getting a pop-up.
[Disclosure Process]
- Reported the Vulnerability to the WordPress Team.
- Acknowledged confirmed from the Vendor that vulnerability exist.
- CVE has been assigned by WPScan.
- Vendor confirm that the vulnerability is fixed or a latest version, patch is released.
- Vulnerability disclosed to the public.
[Reference]
https://wpscan.com/vulnerability/9ebdd1df-1d6f-4399-8b0f-77a79f841464
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-24681
[Has vendor confirmed or acknowledged the vulnerability?]
Yes
[Discoverer]
Nikhil Kapoor from eSecForte Technologies Pvt Ltd
