

Here is Everything you should know about HTML INJECTION IN EMAIL
WHAT IS HTML INJECTION?
HTML injection is a type of injection issue that occurs when a user is able to control an input point and is able to inject arbitrary HTML code into a vulnerable web page. It can be used to deface a web page or redirect the user to a malicious website. It can also be chained with other vulnerabilities to increase the impact for it.
WHAT IS CONTENT SPOOFING?
According to OWASP, Content Spoofing, which is also referred to as text injection, is a type of attack that is possible when an application does not properly handle the user-supplied data, enabling an attacker to supply content to a web application, via a parameter value, that is reflected back.
PROOF OF CONCEPT FOR HTML INJECTION IN EMAIL:
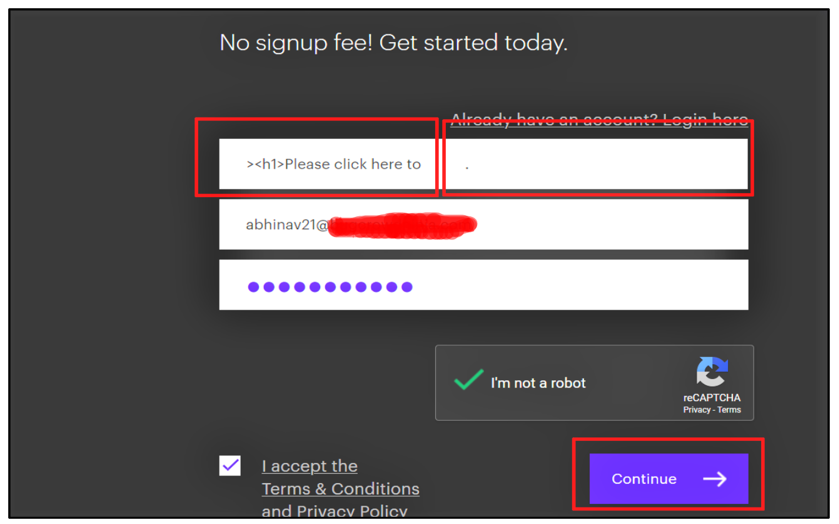
There was a Create New Account Page on the application. On submitting the details, an email was sent to the user. While analysing the application behavior, HTML Injection(Content Spoofing) in Email was found. The steps were as follow:
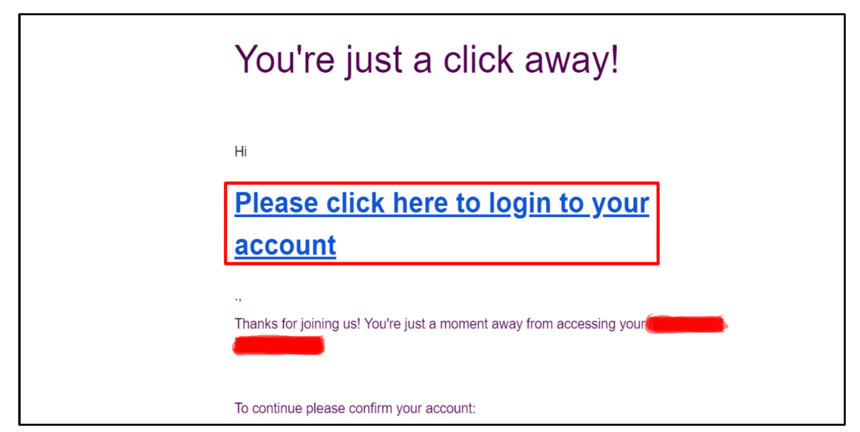
1.Open the Create New Account Page of the application, enter your email id and Password. In the First Name parameter, HTML Injection payload ( <a href=”attacker.com”><h1>Please click here to login to your account<h1></a> ) is inserted.
2. A new mail is sent to the user, where the payload is successfully executed.
IMPACT:
The impact for this type of attack would depend upon the type of application or the type of business the organisation is involved with. It can lead to phishing attacks. For banking applications, this attack becomes critical.
The perfect parameter for testing this type of attack would be “invite new user” parameters.
OWASP Reference: https://owasp.org/www-community/attacks/Content_Spoofing
RECOMMENDATION:
It is important to validate the data supplied by the user, along with output encoding.
Prepared By:- Abhinav Khanna
Reviewed By:- Vaibhav Rai
Approved By:- Saurabh Seth

